OpenShift Container Platform
- OpenShift
- OpenShift Streaming and Training
- OpenShift on Public Cloud
- Blogs
- Meetings
- Differences in developing on OpenShift as opposed to other Kubernetes distributions
- Red Hat’s approach to Kubernetes. Standardization
- OpenShift.io online IDE
- OC CLI Auto Completion
- Cluster Autoscaler in OpenShift
- e-Books
- Online Learning
- Local Installers
- Cloud Native Development Architecture. Architectural Diagrams
- Cluster Installers
- Networking (OCP 3 and OCP 4)
- Security
- Openshift Compliant Docker Images
- IBM Cloud Paks and OpenShift
- OpenShift on AWS
- OpenShift Dedicated
- Other Awesome Lists
OpenShift
- Wikipedia.org: OpenShift
- OpenShift.com
- OpenShift blog 🌟
- docs.openshift.com 🌟
- developers.redhat.com 🌟
- github.com/openshift/origin 🌟 Images for OpenShift 3 and 4 - see openshift/okd for more
- try.openshift.com 🌟 Create an OCP (OpenShift Container Platform) Cluster or OSD (OpenShift Dedicated) Cluster.
- okd.io The Community Distribution of Kubernetes that powers Red Hat OpenShift.
- OpenShift Commons Where users, partners, customers, and contributors come together to collaborate and work together on OpenShift. Commons builds connections and collaboration across OpenShift communities, projects and stakeholders.
- twitter.com/openshift
- OpenShift in DockerHub
- reddit.com/r/openshift
- reddit.com/r/redhat
OpenShift Streaming and Training
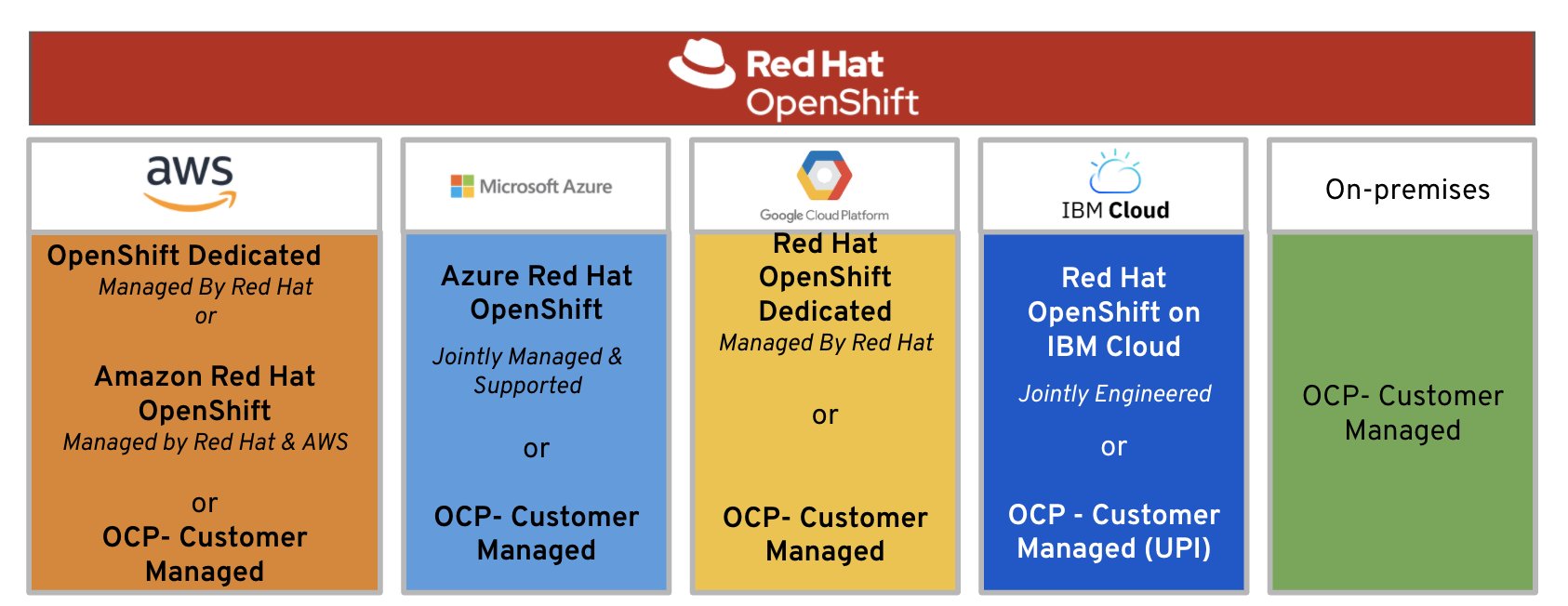
OpenShift on Public Cloud
- OCP4 on AWS: ref1 , ref2
- OpenShift Dedicated - Price lowered by 75% on average, SLA improved to 99.95% 🌟
- Amazon Red Hat OpenShift
- OpenShift on Google Cloud
- Microsoft Azure Red Hat OpenShift
- Red Hat OpenShift on IBM Cloud
- OpenShift Online
- OpenShift.io
- Developer Sandbox
- Red Hat Marketplace
Azure Red Hat OpenShift ARO
Blogs
Meetings
Differences in developing on OpenShift as opposed to other Kubernetes distributions
Red Hat’s approach to Kubernetes. Standardization
| Reference | Author | URL |
|---|---|---|
| “Given the difficulty of navigating the cloud-native ecosystem, especially the one around Kubernetes, there is a high demand for easy-to-administer development platforms that deliver applications in Kubernetes-managed containers.” | OMDIA | Red Hat’s approach to Kubernetes |
| Industry momentum has aligned behind Kubernetes as the orchestration platform for Linux® containers. Choosing Kubernetes means you’ll be running the de facto standard regardless of which cloud environments and providers are in your future. | CNCF Survey 2019 | Red Hat’s approach to Kubernetes |
| “It’s not just enough to do Kubernetes. You do need to do CI/CD. You need to use alerting. You need to understand how the security model of the cloud and your applications interplay.” | Clayton Coleman,Senior Distinguished Engineer, Red Hat | Red Hat’s approach to Kubernetes |
| “Kubernetes is scalable. It helps develop applications faster. It does hybrid and multicloud. These are not just technology buzzwords, they’re real, legitimate business problems.” | Brian Gracely,Director, Product Strategy, Red Hat OpenShift | Red Hat’s approach to Kubernetes |
| “Our job is to make it easier and easier to use, either from an ops point of view or a developer point of view—while acknowledging it is complex, because we’re solving a complex problem.” | Chris Wright,Chief Technology Officer, Red Hat | Red Hat’s approach to Kubernetes |
OpenShift.io online IDE
- openshift.io 🌟 an online IDE for building container-based apps, built for team collaboration.
OC CLI Auto Completion
Cluster Autoscaler in OpenShift
- OpenShift 3.11: Configuring the cluster auto-scaler in AWS
- OpenShift 4.4: Applying autoscaling to an OpenShift Container Platform cluster
e-Books
- O’Reilly Free Book: DevOps with OpenShift
- O’Reilly Free Book: Openshift for developers
- O’Reilly: Free ebook: Kubernetes Operators: Automating the Container Orchestration Platform
- Manning: Openshift in action
- Packt publishing: Learn Openshift
- O’Reilly: Free ebook: Knative Cookbook: Building Effective Serverless Applications with Kubernetes and OpenShift
- redhat.com Free ebook: Container Storage for Dummies
Kubernetes e-Books
Online Learning
- learn.openshift.com 🌟 Interactive Learning Portal
- katacoda.com 🌟 Interactive Learning and Training Platform for Software Engineers
- redhatgov.io
- udemy.com: Red Hat OpenShift With Jenkins: DevOps For Beginners
- udemy.com: OpenShift Enterprise v3.2 Installation and Configuration
- udemy.com: Ultimate Openshift (2018) Bootcamp by School of Devops 🌟 With Openshift Origin 3.10 / OKD 2018, Kubernetes, Jenkins Pipelines, Prometheus, Istio, Micro Services, PaaS
- Udemy: OpenShift 4 desde cero 🌟
Local Installers
- developers.redhat.com: Red Hat Container Development Kit
- A few other options to use OKD locally include oc cluster up and minishift. These may be a better fit for your use case if you only need a quick throwaway environment.
- github.com/redhatdemocentral: OpenShift Container Platform Install Demo 🌟
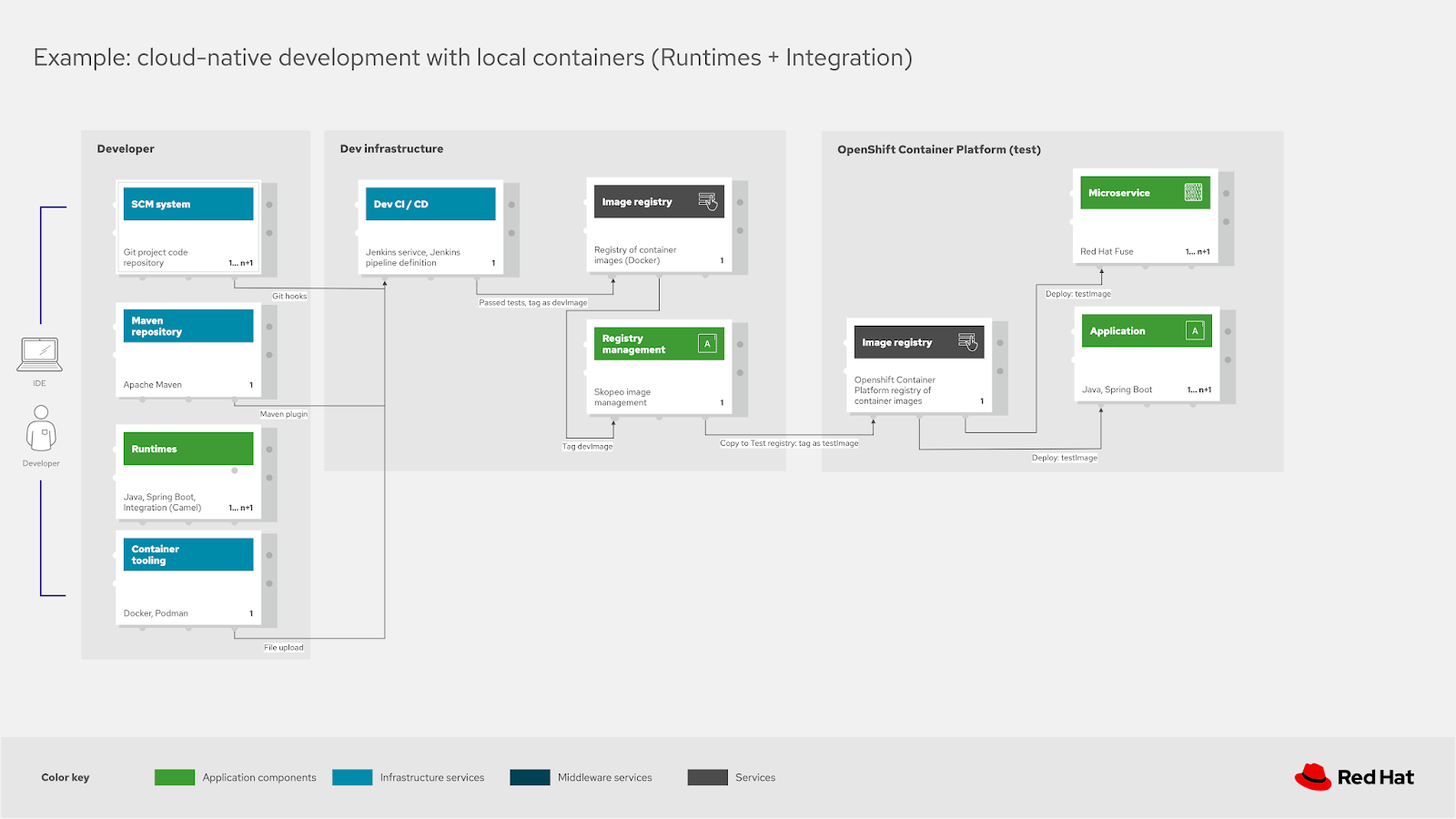
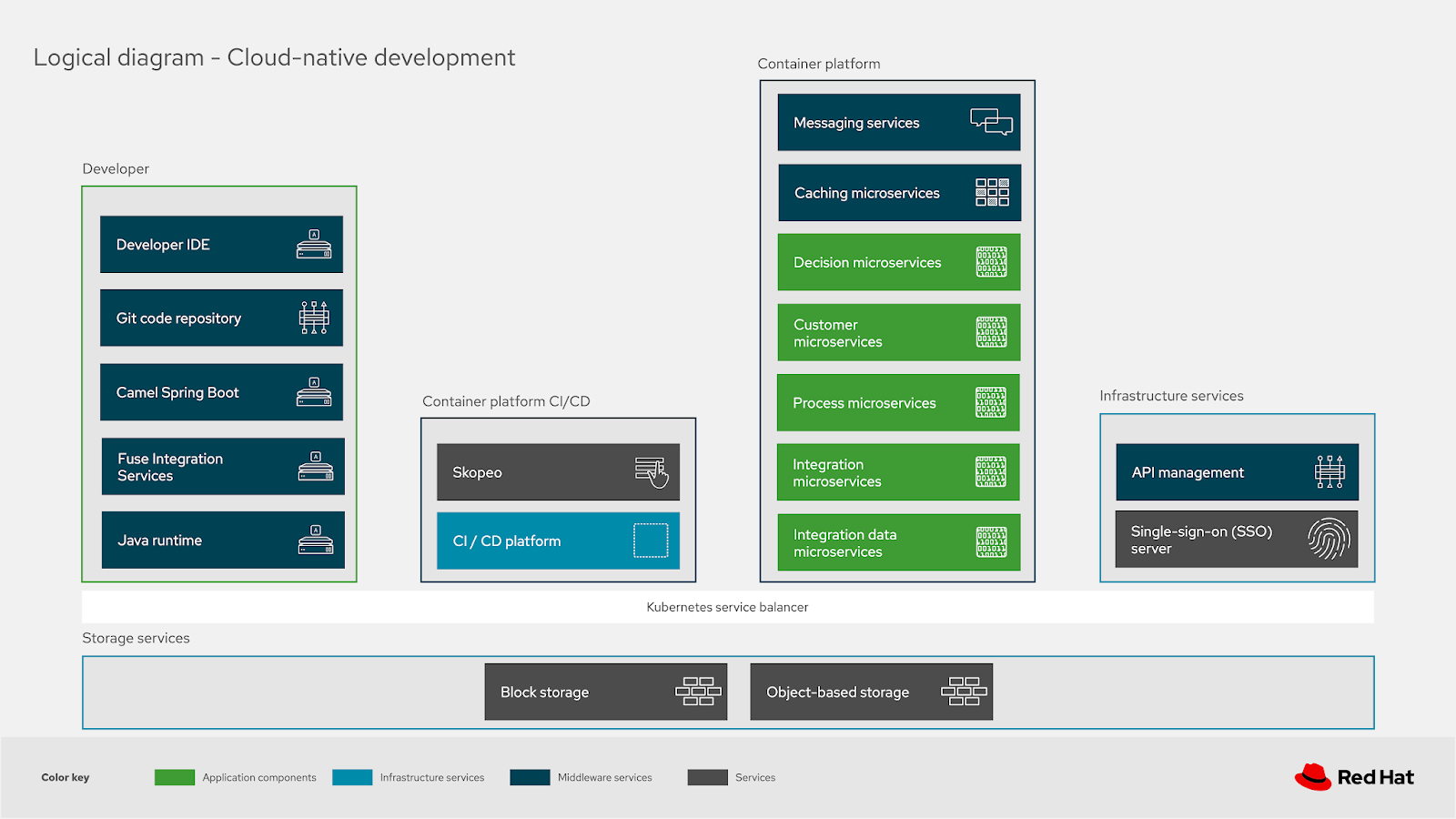
Cloud Native Development Architecture. Architectural Diagrams
- Cloud-native development is an approach to building and running applications to fully exploit the advantages of the cloud computing model (i.e. responsive, elastic and resilient applications).
- Dzone: Cloud-native development - A blueprint 🌟 These architectural blueprints are providing you with a way to implement a solution using open source technologies focusing on the integrations, structures and interactions proven to work.
- Dzone: Cloud-Native Development - Common Architectural Elements 🌟
- Dzone: Cloud-native development - An advanced deployment blueprint 🌟
- Portfolio Architecture WorkShops 🌟 Workshops for creating impactful architectural diagrams. This workshop will teach you how to use, design, and create architectural diagrams based on the draw.io tooling and Red Hat Portfolio Architecture design elelements. You’ll leverage existing portfolio architecture diagrams as starting points.
- Portfolio Architecture Tooling
- gitlab.com: Portfolio Architecture Examples
Cluster Installers
OKD 3
- OKD.io: The Community Distribution of Kubernetes that powers Red Hat OpenShift.
- blog.openshift.com: Installing OKD 3.10 on a Single Host 🌟
- youtube.com: OpenShift Origin is now OKD. Installation of OKD 3.10 from start to finish
- Install RedHat OKD 3.10 on your development box: This repository is a set of scripts that will allow you easily install the latest version (3.10) of OKD in a single node fashion. What that means is that all of the services required for OKD to function (master, node, etcd, etc.) will all be installed on a single host. The script supports a custom hostname which you can provide using the interactive mode.
- docs.okd.io: Planning your installation
OpenShift 3
- belgium.devoteam.com: Using Ansible Tower to deploy OpenShift 3 on Azure: a step-by-step guide
- uncontained.io: Installing a Highly Available OpenShift Cluster 🌟
OpenShift 4
- github.com/openshift/installer openshift installer 🌟
- CI/CD Pipeline to deploy OpenShift Container Platform 4.x to AWS 🌟
- blog.openshift.com: 9 steps to awesome with kubernetes openshift
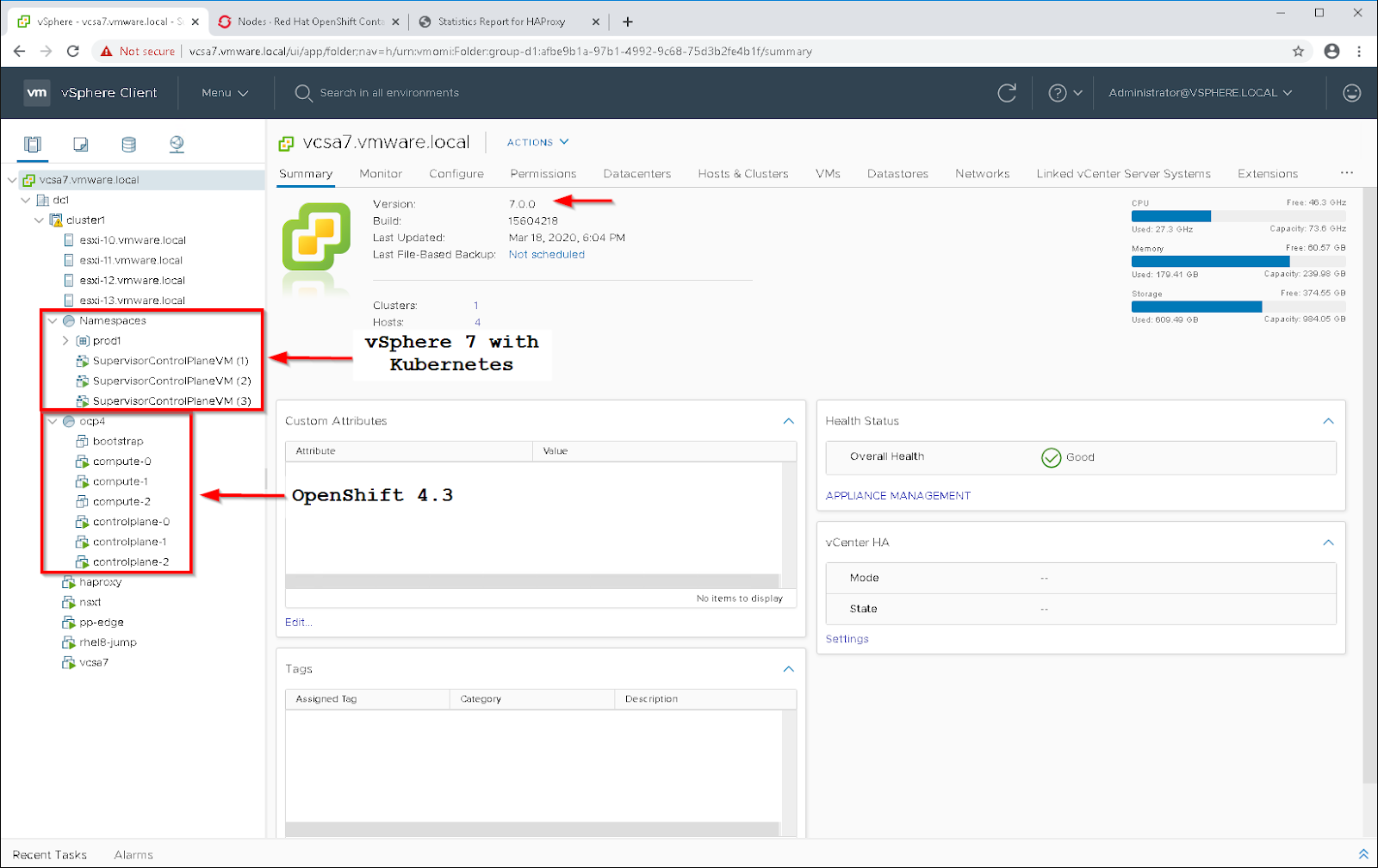
OpenShift 4 deployment on VMWare vSphere
- blog.openshift.com: OpenShift 4.2 vSphere Install Quickstart
- blog.openshift.com: OpenShift 4.2 vsphere install with static IPs 🌟
- youtube: Deploy OpenShift 4 to vSphere using OpenShift’s UPI
Deploying OpenShift 4.4 to VMware vSphere 7
Networking (OCP 3 and OCP 4)
- Using sidecars to analyze and debug network traffic in OpenShift and Kubernetes pods
- developers.redhat.com: Skupper.io: Let your services communicate across Kubernetes clusters
- blog.openshift.com: Troubleshooting OpenShift network performance with a netperf DaemonSet
- blog.openshift.com: Advanced Network customizations for OpenShift Install
Security
How is OpenShift Container Platform Secured?
- docs.openshift.com: OpenShift 3 Overview
- docs.openshift.com: OpenShift 3 Securing the Container Platform
- ocs.openshift.com: OpenShift 4 Understanding Authentication
Security Context Constraints
- docs.openshift.com: Managing Security Context Constraints
- docs.openshift.com: Managing Security Context Constraints. Security Context Constraints
- Dzone: Understanding OpenShift Security Context Constraints
Review Security Context Constraints
- Security Context Constraints (SCCs) control what actions pods can perform and what resources they can access.
- SCCs combine a set of security configurations into a single policy object that can be applied to pods. These security configurations include, but are not limited to, Linux Capabilities, Seccomp Profiles, User and Group ID Ranges, and types of mounts.
- OpenShift ships with several SCCs. The most constrained is the restricted SCC, and the least constrained in the privileged SCC. The other SCCs provide intermediate levels of constraint for various use cases. The restricted SCC is granted to all authenticated users by default.
- The default SCC for most pods should be the restricted SCC. If required, a cluster administrator may allow certain pods to run with different SCCs. Pods should be run with the most restrictive SCC possible.
- Pods inherit their SCC from the Service Account used to run the pod. With the default project template, new projects get a Service Account named default that is used to run pods. This default service account is only granted the ability to run the restricted SCC.
- Recommendations:
- Use OpenShift’s Security Context Constraint feature, which has been contributed to Kubernetes as Pod Security Policies. PSPs are still beta in Kubernetes 1.10, 1.11, and 1.12.
- Use the restricted SCC as the default
- For pods that require additional access, use the SCC that grants the least amount of additional privileges or create a custom SCC Audit
- To show all available SCCs:
oc describe scc - To audit a single pod:
oc describe pod <POD> | grep openshift.io\/scc - Remediation: Apply the SCC with the least privilege required
OpenShift Network Model & Network Policy
- docs.openshift.com: Understanding networking
- NetworkPolicies and Microsegmentation
- Fully Automated Management of Egress IPs with the egressip-ipam-operator 🌟
- GitHub: redhat-cop OpenShift Toolkit Network Policy 🌟
- redhat.com: Network traffic control for containers in Red Hat OpenShift 🌟
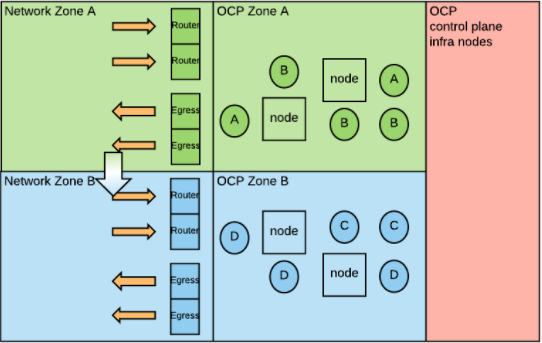
Network Security Zones
- stackoverflow.com: Is that possible to deploy an openshift or kubernetes in DMZ zone? 🌟
- OpenShift and Network Security Zones: Coexistence Approaches 🌟🌟🌟
- Introduction: Kubernetes and consequently OpenShift adopt a flat Software Defined Network (SDN) model, which means that all pods in the SDN are in the same logical network. Traditional network implementations adopt a zoning model in which different networks or zones are dedicated to specific purposes, with very strict communication rules between each zone. When implementing OpenShift in organizations that are using network security zones, the two models may clash. In this article, we will analyze a few options for coexistence. But first, let’s understand the two network models a bit more in depth.
- Network Zones have been the widely accepted approach for building security into a network architecture. The general idea is to create separate networks, each with a specific purpose. Each network contains devices with similar security profiles. Communications between networks is highly scrutinized and controlled by firewall rules (perimeter defense).
- Conclusion: A company’s security organization must be involved when deciding how to deploy OpenShift with regard to traditional network zones. Depending on their level of comfort with new technologies you may have different options. If physical network separation is the only acceptable choice, you will have to build a cluster per network zone. If logical network type of separations can be considered, then there are ways to stretch a single OpenShift deployment across multiple network zones. This post presented a few technical approaches.
OpenShift Route and OpenShift Ingress
- openshift.com: Kubernetes Ingress vs OpenShift Route
- Ingress Operator in OCP 4
- cloud.ibm.com: OpenShift Ingress
OpenShift Egress
- Accessing External Services Using Egress Router
- How to Enable Static Egress IP in OCP
- dzone: OpenShift Egress Options Network security is a crucial part of any of Software as a Service type business. Read on to see how to implement OpenShift to create better network security.
Openshift Compliant Docker Images
- Red Hat Container Catalog - RedHat Registry (registry.redhat.io) 🌟 License required
- DockerHub OpenShift
- github.com/sclorg/
- github.com/sclorg/postgresql-container/
- github.com/sclorg/mariadb-container
Gitlab
Atlassian Confluence6
Sonatype Nexus 3
Rocket Chat
- Deploying Rocket.Chat on OpenShift
- opensource.com: Why choose Rocket.Chat for your open source chat tool
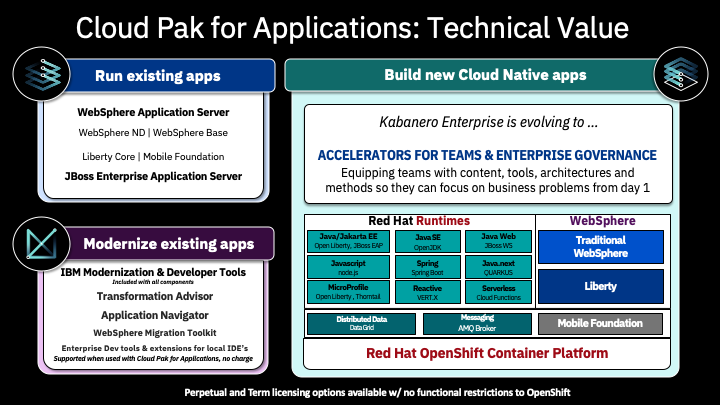
IBM Cloud Paks and OpenShift
- cloudpak8s.io
- What are IBM Cloud Paks? Beyond containers and Kubernetes, enterprises need to orchestrate their production topology, and to provide management, security and governance for their applications. They need to do this while improving efficiency and resiliency, reducing costs and maximizing ROI.
- IBM Cloud® Paks are enterprise-ready, containerized software solutions that give clients an open, faster and more secure way to move core business applications to any cloud. Each IBM Cloud Pak® includes containerized IBM middleware and common software services for development and management, on top of a common integration layer — designed to reduce development time by up to 84 percent and operational expenses by up to 75 percent. IBM Cloud Paks run wherever Red Hat® OpenShift® runs and are optimized for productivity and performance on Red Hat OpenShift on IBM Cloud.
- IBM Cloud Pak Playbook The Cloud Pak for Applications provides product offerings to support modernizing existing applications and building new cloud native applications. The applications run within a Kubernetes cluster provided with the Red Hat OpenShift Container Platform. The focus provided here is on running application workloads as containers. The Cloud Pak for Applications is a bundle of multiple offerings. This diagram provides an overview of what offerings are included and what they would be used for:
OpenShift on AWS
- blog.openshift.com: AWS and red hat quickstart workshop
- aws.amazon.com: AWS Quick Start (OpenShift 3.11 on AWS) View deployment guide
- openshift.com: Introducing Red Hat OpenShift Service on AWS
OpenShift Dedicated
- OpenShift Dedicated 🌟
- Bringing OpenShift Dedicated to Life at Red Hat
- Red Hat OpenShift Dedicated price reduction: Price lowered by 75% on average, SLA improved to 99.95% 🌟